- Why Heresafe?
- PricingWe don’t hide behind fancy sales teams before we tell you, our prices.
- Clients
See who we are working with and what they have to say about Heresafe.- Resources
Check out our blog, useful guides, whitepapers and product videos.- Prequalification and Induction Guide
- Contractor Compliance Guide
- Mini-Audit your Permit to Work System
- Health and Safety Audit Checklist
- Resource Library
- Blog
Book a demo
High-Security Access Control: Managing Subcontractors and Visitors in Restricted Government Environments
Did you know that the UK’s National Cyber Security Centre handled 204 nationally significant cyber incidents between September 2024 and August 2025, a record high representing an almost 130% increase from the previous year?
While cyber threats dominate headlines, physical security in restricted government environments remains equally critical, as unauthorised or poorly managed access by subcontractors and visitors can enable insider risks, data compromise, or breaches of classified assets. In high-security UK government sites, from MoD facilities to secure government buildings, stringent controls over temporary personnel are essential to protect national interests, comply with frameworks like national security vetting, and mitigate vulnerabilities in dynamic access scenarios.
Key Areas We Will Cover
- The unique security demands of restricted government environments in the UK
- Key challenges in managing subcontractors and visitors under high-security protocols
- Essential best practices for robust access control and verification
- Core features of digital systems tailored for government-restricted access
- How Heresafe supports secure, compliant management in sensitive settings
- Practical steps to implement enhanced controls
Introduction
High-security access control in restricted government environments focuses on tightly managing subcontractors and visitors to prevent unauthorised entry, ensure compliance with national security standards, and maintain audit-ready records. These sites demand rigorous vetting, real-time tracking, and role-based permissions to safeguard classified information, critical infrastructure, and personnel. With evolving threats and regulatory expectations, including national security vetting processes overseen by UKSV, effective digital solutions are vital for balancing security with operational needs. This guide outlines proven strategies and illustrates how Heresafe’s platform delivers centralised, automated tools to streamline subcontractor and visitor management in these high-stakes settings.
Understanding High-Security Access Control in Restricted Government Environments
Restricted government environments, such as MoD sites, secure facilities, and other protected premises, operate under strict protocols where access is limited to authorised individuals with appropriate clearances.
Unique Challenges: Subcontractors and Visitors in Sensitive Sites
Subcontractors and visitors introduce heightened risks due to temporary status, varying clearance levels, and the need for escorted or zoned access.
Common challenges include:
- Ensuring personnel screening and vetting requirements are met, from BPSS pre-employment screening through to national security vetting where required, such as SC or DV.
- Preventing insider threats or unauthorised access in areas with public interfaces and restricted zones
- Managing escort requirements, pre-approvals, and real-time monitoring to avoid tailgating or unaccompanied movement
- Maintaining detailed audit trails to support internal security oversight, contract requirements, and evidence of who was approved, expected, and on site.
- Coordinating multi-site or irregular access without creating data silos or delays in high-throughput scenarios
These issues amplify exposure to security breaches, non-compliance penalties, and operational disruptions, highlighting the need for integrated digital controls.
Essential Best Practices for High-Security Access Control
Robust management combines pre-vetting, real-time verification, and continuous oversight to uphold stringent standards.
Pre-Engagement and Vetting: Establish Rigorous Foundations
Require advance submission and verification aligned with government protocols.
- Collect security clearance evidence, insurance, right-to-work details, and sponsor approvals via secure channels
- Automate workflows for cross-checking against watchlists, blacklists, or vetting databases
- Issue time-limited, role-specific permissions with escort mandates where required
Real-Time Check-Ins and Verification: Ensure Controlled Entry
Implement immediate validation at entry points to confirm identity and permissions.
- Use kiosk or mobile check-ins with photo ID capture, QR codes, or biometric options for high-security zones
- Verify against pre-approved records, clearance status, and current on-site requirements in real time
- Enforce geo-tagged logging and zone restrictions to track movements accurately
Ongoing Monitoring and Compliance: Sustain Audit-Ready Oversight
Maintain dynamic control throughout the visit or contract period.
- Trigger automated reminders for clearance renewals, training, or policy acknowledgements
- Link access rights to verified status with instant revocation for expiries or issues
- Provide role-based dashboards showing on-site status, expected personnel, and compliance alerts
Integration and Reporting: Deliver Comprehensive Visibility
Connect access data to broader security systems for full accountability.
- Generate real-time overviews of who is on site, including escorts and restricted zone access
- Set alerts for anomalies, such as unaccompanied movement or overdue check-outs
- Produce exportable, time-stamped audit trails to support investigations or regulatory reviews
These practices minimise risks, accelerate compliant access, and strengthen defences in restricted environments.
How Heresafe Enhances High-Security Access Control
Heresafe’s cloud-based platform addresses government-specific needs with automated, traceable tools that centralise subcontractor and visitor management.
Relevant Features for Restricted Environments
- Self-Service Portal: Subcontractors and visitors submit documents, complete questionnaires, and acknowledgements remotely, ensuring pre-approval and reducing on-site delays
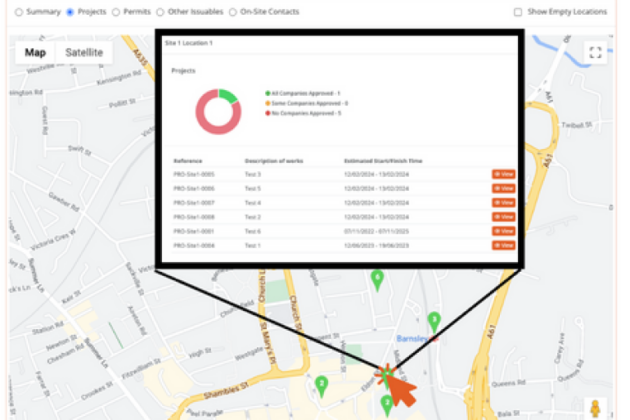
- Real-Time Check-Ins and Geo-Tagged Tracking: Mobile or kiosk sign-ins provide instant confirmation, with “On-Site Now” dashboards offering visibility across sites and zones
- Automated Credential and Compliance Management: Expiry alerts, approval chains, and linked permissions keep records current and aligned with vetting requirements
- Integrated Reporting and Audit Tools: Time-stamped logs, policy acknowledgements, and role-based access support stronger internal governance, clearer audit trails, and audit readiness
Proven Impact
Heresafe supports organisations operating in complex and security-conscious environments, including KBR Aspire Defence, by providing the approvals, audit trails, and real-time visibility needed to reduce manual processes and maintain control during peak or irregular activity.
Conclusion
High-security access control in restricted government environments relies on meticulous management of subcontractors and visitors through vetting, real-time verification, and audit trails. By tackling challenges like clearance compliance and insider risks with digital processes, organisations achieve enhanced protection, regulatory alignment, and operational resilience. Heresafe empowers teams to implement these measures effectively, transforming potential vulnerabilities into robust, defensible safeguards.
Ready to Strengthen High-Security Access Control?
Elevate visitor and subcontractor management with Heresafe. Book a demo to see if Heresafe is right for you.
Book a demoFind out if you’re ready with our Heresafe Onboarding Kit
Unsure if Heresafe is the right fit? We understand that choosing a new system can be challenging. That’s why we’ve developed our Onboarding Kit to simplify the decision-making process.
Check our package details
No matter which package you choose, you'll receive the best features tailored for you and your team, to achieve your automation and management goals. Find more details on the available packages.
Make it your own
You’ll get to see and choose your customisation options, and check out the available add-ons and extras so the system is exactly what you want and need.
Getting you started and seeing value
Keeping this guide with you, and working closely with us, we can walk you through onboarding so you can be completely up and running with your own Heresafe system.
It’s easy to get started.
Step 1
Book a demo of Heresafe with the team.
Step 2
We’ll chat through your requirements and see if Heresafe is right for you.
Step 3
We’ll send you demo access and our onboarding kit to help you decide what you need.
Step 4
You decide if we’re right for you. No pushy sales calls.
Step 5
Like what you see and hear? Let’s get you onboarded with Heresafe!
- Clients